The development of information technology has been synonymous with the increased share of multimedia traffic in data networks. At the same time, the trend has necessitated the need to solve a myriad of security issues in relation to data. For instance, organizations must now implement measures to protect against leakage of sensitive information and identify the source of a leak. Besides, they need ways to block unauthorized data changes and protect digital objects’ copyright. In this context, companies can use methods of steganography, digital signature and watermarking to implement embedding in digital objects visible or hidden information sequences for different purposes.
Steganography and watermarking are particularly relevant for a range of data, particularly documents. This article deals with steganography and watermarking methods, the techniques, their differences, and when to use them. The topic of digital signatures will be covered in detail in our next article.
What is Steganography?
Steganography is the practice of hiding a secrete message inside an ordinary, non-secret file or message. Currently, steganography involves embedding a secret piece of text inside of an image or hiding a secret message or script in an Excel or Word document. The process allows the sender to avoid detection, and the receiver extracts the secret data at its destination.
Steganography should not be confused with cryptography since it does not scramble plaintext into ciphertext using a key. Instead, the process is purely a form of data hiding that you can execute in various clever ways. Cryptography involves data encryption and decryption for privacy purposes, while steganography involves data hiding to enable deceit and secrecy. Occasionally, people combine steganography with encryption as an extra step for data protection.
Modern Digital Steganography
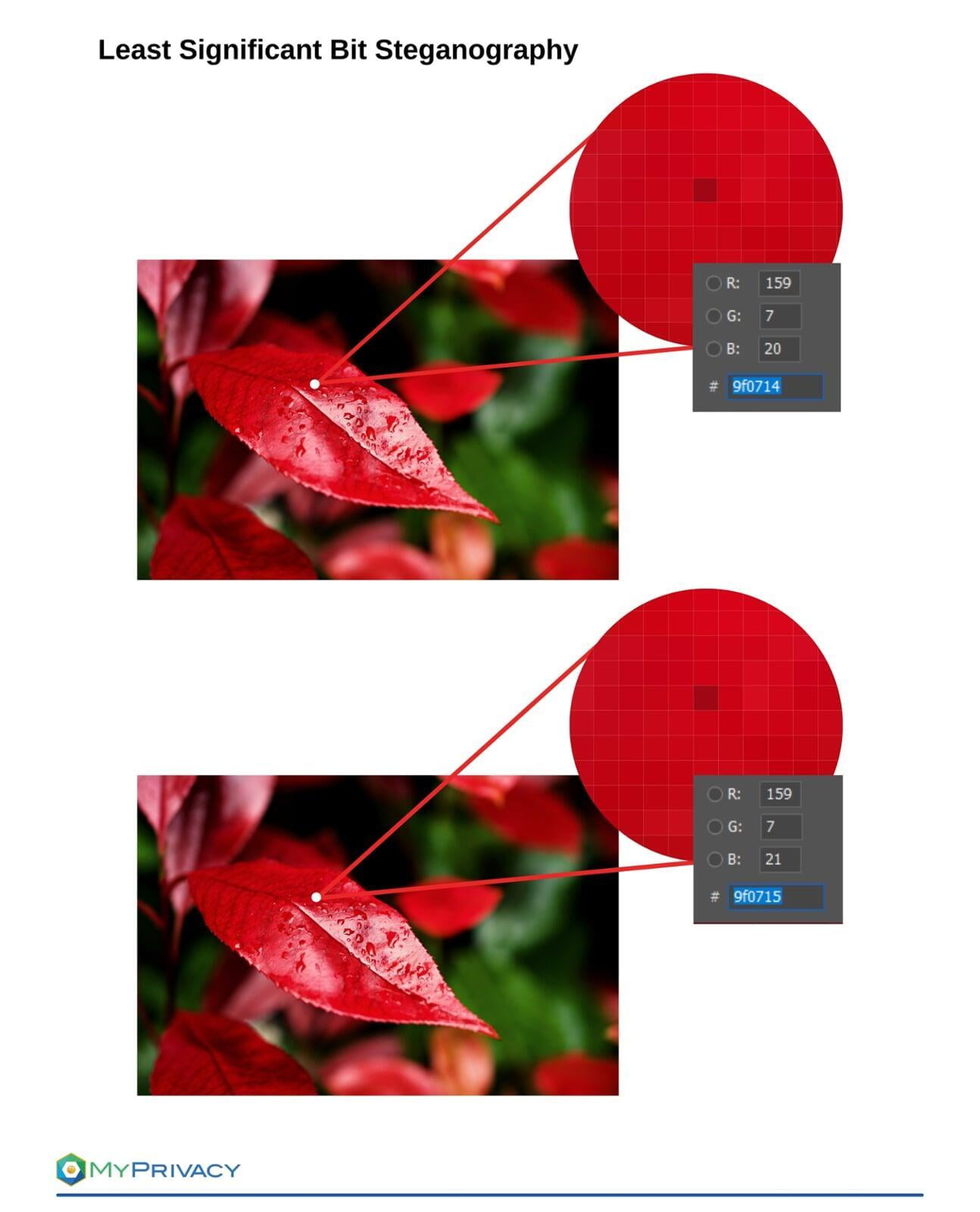
In modern steganography, data is first obfuscated or encrypted somehow, and an algorithm inserts the data into a non-secret, ordinary file format, like video, audio, images or other file types. How is this process possible? You can embed secret data into ordinary documents in various ways. Mainly, users hide data in bits representing the same color pixels repeated in a row in an image file. Applying encrypted data to this redundant data in an inconspicuous way results in a file that appears identical to an original one but has ‘noise’ patterns of regular unencrypted data.
The integrity of hidden information, once embedded within the stego object, must be preserved. A stego object is the cover message that hosts the embedded data in steganography. In this process, the message should not change in any manner, including information being added or lost. If the stego object is modified after the steganography process (e.g. image processing, compression etc.), it will defeat the technique’s purpose. After receiving the secret message, the receiver should dispose of the cover message (stego object) to prevent accidental reuse.
Steganography Software
Depending on the type of the cover message, steganography software perform different functions to hide data. For instance, steganography tools based on text files encode hidden information as whitespaces at the end of lines in a document. The tools can also encrypt data before hiding it and allow only intended recipients to retrieve the message.
Beside commercial products the steganography market consists of a lot of open source solutions. A prime example is the OpenStego open-source steganography tool that can hide any data within a cover file and watermark it with an invisible signature. Using OpenStego, you can perform steganography effectively with image files of different types, including JPEG, JPG, BMP, GIF, and PNG. OpenStego watermarking provides an authority to imprint invisible watermark on the image file. Xiao Steganographyis another free tool that you can use to hide secret files in the image (BMP) as well as audio files (WAV). Additionally, the hybrid steganography tool allows you to encrypt hidden files with a variety of supported encryption algorithms, including 3DES and RC4, and hashing algorithms like MD5 and SHA.
What is the purpose of Steganography?
Organizations use steganography mainly to conceal and deceive. A recent research paper states that the main idea behind steganographic methods is to make embedded information invisible to an attacker. The process allows users to safely transmit secret digital content, including text, image, audio, and video content.
While there are numerous benefits and legitimate uses of steganography, cyberattacks have also discovered they can leverage the technology to obscure the transmission of malicious software.
What is Watermarking?
Digital watermarking is a method of embedding data into digital multimedia content. The process helps users verify the credibility of the content or to identify the identity of the digital content’s owner. Digital watermarking can either be visible or invisible. In the visible method, the watermark can be a logo or a text that denotes the digital content’s owner or the confidentiality level of the content. Conversely, in invisible watermarking, the embedded data is invisible or inaudible in the case of audio content. This post mainly focuses on visible watermarking in documents.
Once a watermark is embedded in a document, it potentially experiences many attacks while digitally processing a document. Sometimes, the manipulation is unintentional. For instance, an image embedded with a watermark gets affected by low pass filtering or gamma correction or compression. On the other hand, cropping is an intentional risk to watermarking. In effect, watermarks need to be robust to avoid possible attacks. Strong watermarking also preserves the signal quality.
When do you use Digital Watermarking?
Visible watermarks are valuable when used for protecting documents. It becomes more secure since everyone can see the watermark and thus verify the documents authenticity.Watermarks are well established for ensuring authenticity in banknotes, cheques, and important agreements. Mainly, the method provides a way of protecting from forgery. However, this traditional application of watermarks only tells you about the creator but does not contain information about the authorized user.
With digital watermarks, you can identify the authorized recipient as well. Such capabilities have made digital watermarking popular in various areas today, including copyright protection, source tracking, broadcast tracking, and hidden communication. For example, online publishers commonly use the digital watermarking technique to identify the source of media files shared without permission. You can also use watermarking to identify authorized information users and prevent editing or transforming original files without detection.
Steganography vs. Watermarking
Steganography is closely related to watermarking, and more frequently, people use the terms interchangeably. However, the two techniques share some similarities and differences. Steganography and watermarking are information embedding techniques that allow including data in other digital data such as documents. While the purpose of steganography is to hide data in media files like video, audio, still images, and documents for secret message transmission, the aim of watermarking is to protect content from malicious use and deter unauthorized copying.
While steganography makes secret information undetectable, visible watermarking allows anyone to see it. It is essential to ensure watermarking is robust so that intentional and unintentional manipulation would not compromise, remove, or destroy the information in any way in the marked media. On the other hand, fragile watermarks are intended to get destroyed even by minimal modification of the content.
Steganography is used for secret communication by its very nature, whereas watermarking is used for content protection, authentication, and copyright management.
The steganography process hides a message for later retrieval by the intended recipient, preventing external parties from detecting it. In this case, the technique allows secret communication while concealing the existence of a hidden message. An attacker without knowledge of the process cannot detect the message in the document. On the other hand, watermarking conceals data to protect digital media like video, photographs, or audio.